Windows Server 2012 R2 Datacenter Activation Crack
Tor is an encrypted anonymising network that makes it harder to intercept internet communications, or see where communications are coming from or going to. In order to use the WikiLeaks public submission system as detailed above you can download the Tor Browser Bundle, which is a Firefox-like browser available for Windows, Mac OS X and GNU/Linux and pre-configured to connect using the anonymising system Tor. Tails If you are at high risk and you have the capacity to do so, you can also access the submission system through a secure operating system called. Tails is an operating system launched from a USB stick or a DVD that aim to leaves no traces when the computer is shut down after use and automatically routes your internet traffic through Tor. Tails will require you to have either a USB stick or a DVD at least 4GB big and a laptop or desktop computer. Remove traces of your submission If you are a high-risk source and the computer you prepared your submission on, or uploaded it from, could subsequently be audited in an investigation, we recommend that you format and dispose of the computer hard drive and any other storage media you used. In particular, hard drives retain data after formatting which may be visible to a digital forensics team and flash media (USB sticks, memory cards and SSD drives) retain data even after a secure erasure.
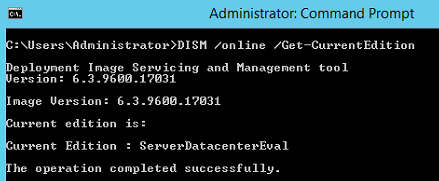
Apr 16, 2015 - Serial Key Windows Server 2012 DataCenter: 48HP8-DN98B-MYWDG-T2DCC-8W83P Datacenter: Y4TGP-NPTV9-HTC2H-7MGQ3-DV4TW. Find serial crack Windows Server 2012 R2 Clef Universelle pour installation de microsoft windows server 2012 R2 version standard, datacenter et Essentials - Activation Key Windows server 2012 R2.
Selecting Technology Review’s is a difficult but rewarding process. Sometimes that transformation comes from developing an entirely new technology, such as that could one day replace silicon devices in microprocessors. We look for people who are tackling important problems in transformative ways. Kak otkritj sejf topaz esli zabil kod 2. We search for candidates around the world who are opening up new possibilities in technology, and then we seek the advice of a before finally selecting the winners. Sometimes it means using existing technologies in novel ways, such as creating an effective way for.
The book Drivers Ed by Caroline B. Cooney, portrays drivers ed, peer pressure, and high school life all in one book. Throughout the book there are two consistent main characters: Rembrandt 'Remey' Marland and Morgan Campbell who fall for each other in the beginning of the book while bonding over some sign stealing. Drivers ed book caroline b cooney summary. Cooney Booklist Caroline B. Cooney Message Board Detailed plot synopsis reviews of Driver's Ed It was a peaceful town, kids playing outside and hardly any crime, until three kids decided to have a little fun not knowing they were committing a crime.
If you used flash media to store sensitive data, it is important to destroy the media. If you do this and are a high-risk source you should make sure there are no traces of the clean-up, since such traces themselves may draw suspicion. This is just a copy and paste job right now. I'll clean this up later.